29 Sep Treat IoT Privacy Like Digital Mayonnaise
Episode 31
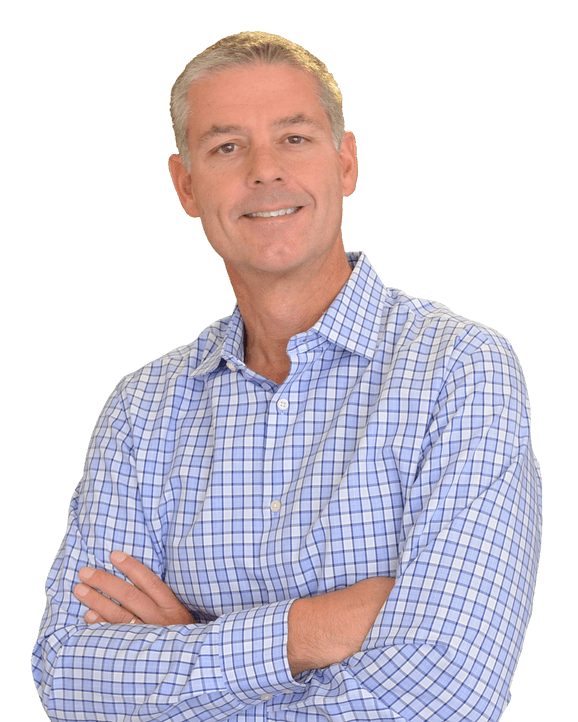
Although an integral part of IoT security, IoT privacy doesn’t rely on technology. It relies instead on self-imposed business rules that govern the way the collected data is used within and outside of the enterprise. As with many things tech, government and law is unable to keep up with the innovation of IoT and with what some call its digital exhaust. In this episode of the IoT Business Show I speak with privacy expert Dale Smith about the top 5 best practices in handling personally identifiable information (PII) and other IoT privacy issues.
In this episode of the IoT Business Show, I speak with privacy expert Dale Smith about the top 5 best practices in handling personally identifiable information (PII) and other IoT privacy issues.
Dale has been an engineer, programmer, banker, entrepreneur, salesman, fund manager, angel investor and retiree. Presently, he’s staff Futurist and Chief Compliance Officer (CCO) at PrivacyCheq – a start-up specialized in privacy solutions for IoT.
As of right now governments around the world have not yet started regulating privacy for the Internet of Things. In the U.S. the FCC has made it clear it would prefer industry to self-regulate but it will take up the slack if necessary. In other parts of the world governments simply have not caught up yet. In any case follow the Golden Rule of privacy, “Do unto other’s data as you would have them do unto yours,” because the blowback from mishandling PII can destroy your brand and balance sheet. And if it’s not the government that regulates, it will be the consumer or the commercial proxy for the consumer that will mold policies or defacto policies following the first inevitable high-profile IoT privacy gaff.
Here’s What We’ll Cover in this Episode
- PII or personally identifiable.
- What does privacy by design mean?
- The tipping point of digital trust.
- The 5 best practices in IoT privacy – one of them is treat security like digital mayonnaise.
- The importance of embracing self-regulation.
- The toxicity of PII.
- The hot potato of data ownership and does it really matter.
Mentioned in this Episode and Other Useful Links
Support this Podcast
If you have been enjoying this podcast, there are a few ways you can support it:
- Share it on social by clicking on the widget on the left or bottom of the page.
- Click here to open iTunes and leave a one-click review or write your thoughts.
- Consider becoming a Certified IoT Professional by enrolling in the ICIP online training program.

Ways to Subscribe to the IoT Business Show
Like what you hear? Subscribe to get each episode delivered to your device via iTunes, Spotify, Google Play, Stitcher Radio or RSS (non-iTunes feed).
Have an opinion? Join the discussion in our LinkedIn group
What do you consider to be the biggest hurdles in IoT privacy?
Click here if you have an opinion on this podcast or want to see the opinion of others