06 Jun The S in IoT Stands for Security
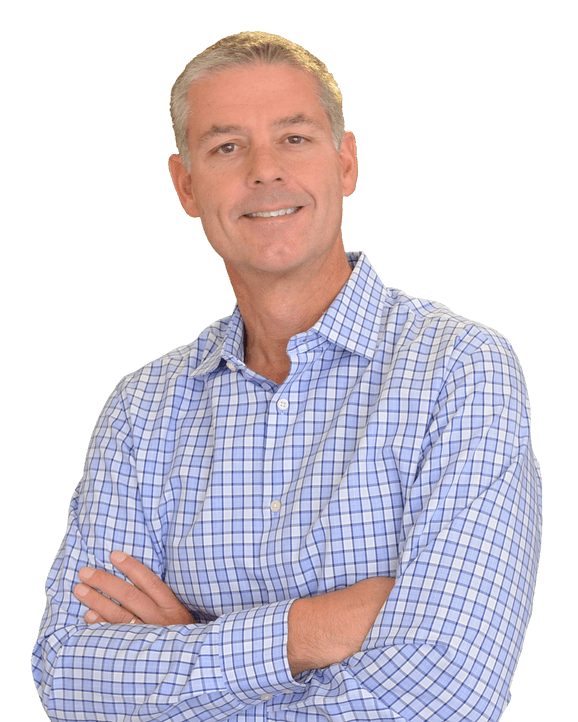
By Chris Romeo
There is a funny joke about IoT that has been shared around Twitter over the past few months. I saw it attributed to a guy named Tim Kadlec (@tkadlec). “The S in IoT stands for security.” Think about that for a second, as you say, “wait, there is no S in IoT”. That is exactly the point of Tim’s statement. IoT is missing security.
It’s not like security and IoT drifted apart as they grew older. Security has never been a foundational element or point of consideration for the IoT. IoT has been about attaching billions of devices to the Internet and the disruption that these devices will create for the world of technology and everyday lives. Without security, this disruption could result in tragedy.
“The S in IoT stands for security.” Think about that for a second, as you say, “wait, there is no S in IoT”. That is exactly the point of Tim’s statement. IoT is missing security.
When I think about security, I think about a fundamental concept called the threat landscape. The threat landscape is the idea that there is a constantly evolving and expanding set of devices, people, and attacks. These entities create an environment where the risk of connecting to a network continues to grow each day. New devices are deployed, new people learn to hack, and new attacks are dreamt up by those hackers. IoT security is the answer to this expanding threat landscape.
The IoT contributes to the threat landscape primarily because of all the new devices that are added daily. Vernon Turner from IDC estimated in 2016 that there were 11 billion devices connected to the Internet, with an expansion to 30 billion by 2020. The IoT is the primary culprit in an additional 20 billion devices. How many of those devices do you think we could say are “secure”?
I’ve identified three reasons why IoT is lacking fundamental security: lack of industry knowledge, lack of developer knowledge, and time to market.
The first is a lack of industry knowledge. Products are being added with IP interfaces that existed previously in a network-less world. When you have a stand-alone device, it is difficult for an attacker to attempt to compromise the device. Physical proximity is a huge security improvement, because it limits who can attempt to attack a device. When an Internet Protocol (IP) interface is added to a device, and it is connected to the Internet, now the device is exposed to the billions of other devices, and to all the bad actors that will attempt to compromise it. The challenge here is that the companies that are moving to IoT are not primarily the same technology companies that have been building security into their products for the past twenty years. Companies such as Cisco, Microsoft, and HPE have decades of security experience. Most of the IoT startups do not. This lack of security knowledge results in products that repeat the same problems of the previous two decades. IoT startups need to learn from industry’s past mistakes.
The second reason the IoT is lacking fundamental security is that the developers do not understand security. Developers are the people writing the code that runs on the IoT devices. They are responsible for ensuring that devices are protected from attacks, both complicated and simple. A perfect example of this is the Mirai botnet, and specifically the XM cameras that made up a large portion of that botnet. The XM cameras are shipped with a default credential, exposed via telnet. A default credential is a user name and password that allow anyone to login to a device across the Internet. Default credentials open a back door. In the Mirai case, that back door allowed malicious software to be loaded on the cameras, and the cameras were then used in a slew of online distributed denial of service (DDoS) attacks. The root cause was developers shipped their cameras and other devices with default credentials.
The third reason is the age-old argument between time to market vs. securing the customer’s environment. Startups are focused on deploying products and features with a velocity that catches the eye of investors and new customers. If a startup does not grow, it dies. Security is something that is not prioritized. Many of the new IoT devices exist in this startup ecosystem, and because of the pressure to ship software and product, security is being placed on the back burner.
The evidence that this problem exists has been largely theoretical thus far, and that is good for us as human beings. Vulnerabilities have been theorized and proven without loss of life, such as the St. Jude’s implantable cardiac devices. The St. Jude’s device is reported to be susceptible to a remote attack through the modification of the Merlin@home transmitter. This could be used to modify programming of an implanted device, and administer inappropriate pacing or shocks to a patient’s heart. A lack of security design and proper security features leave a patient open to an attack that could end their life.
True security reform will only hit IoT when the vulnerability crosses from theoretical to the nightly news. My task is to be a herald for security, and raise awareness of the issues in hopes that they will be fixed prior to anything catastrophic occurring. There are others out there doing this same thing. I Am the Cavalry is an organization focused on improving the security state of IoT.
The solution to this problem is to build security in to everything that is created on the IoT. I’m not a big fan of regulation, but I don’t see any other way to enforce the security properties that we must require in IoT devices. I know that Secure Development Lifecycle (SDL) is the overall solution to this challenge, but I don’t see vendors lining up to take on more work for the “good of society”. They should, but for whatever reason they do not. Regulation and testing is the only way to ensure that the life altering devices that are multiplying by the second do not become do more damage than good. Perhaps there is a door opening for startups that take security seriously?
Chris Romeo is CEO and Security Culture Hacker at Security Journey. His passion is to bring security culture change to all organizations, including their IoT story.
Have an opinion? Join the discussion in our LinkedIn group
Why did IoT forget the security?
Click here if you have an opinion on this podcast or want to see the opinion of others